- Service Configuration for Anthos
- Table of Contents
- Environment variables
- Common properties for all environments
- For Mappers to activate drivers
- Requirements for requests
- Configuring mappers Datasources
- For OQM RabbitMQ
- Exchanges and queues configuration
- Interaction with message brokers
- Specifics of work through PULL subscription
- Keycloak configuration
Service Configuration for Anthos
Table of Contents
- Environment variables
- Requirements for requests
- Configuring mappers Datasources
- Interaction with message brokers
- Keycloak configuration
Environment variables
Common properties for all environments
| name | value | description | sensitive? | source |
|---|---|---|---|---|
APP_ENTITLEMENTS |
ex https://entitlements.com/entitlements/v1
|
Entitlements API endpoint | no | output of infrastructure deployment |
APP_REGISTER |
ex https://register.com/api/register/v1
|
Storage API endpoint | no | output of infrastructure deployment |
APP_PROJECT |
ex opendes
|
Google Cloud Project Id | no | output of infrastructure deployment |
PARTITION_API |
ex http://localhost:8081/api/partition/v1
|
Partition service endpoint | no | - |
SERVICE_TOKEN_PROVIDER |
ex GCP or OPENID
|
Service token provider | no | - |
System Environment required to run service
| name | value | description | sensitive? | source |
|---|---|---|---|---|
SPRING_PROFILES_ACTIVE |
anthos |
spring active profile | no |
For Mappers to activate drivers
| name | value | description |
|---|---|---|
| OQMDRIVER | pubsub | to activate OQM driver for Google PubSub |
| OQMDRIVER | rabbitmq | to activate OQM driver for Rabbit MQ |
Requirements for requests
Record identifiers cannot contain a space character. At the same time, they may contain a % character, which, when combined with subsequent numeric characters, may cause the application to misinterpret that combination. For example, the "%20" combination will be interpreted as a space " " character. To correctly transfer such an identifier, you should additionally perform the url-encode operation on it. This functionality can be built into the front-end application, or you can use an online url-encoder tool ( eg.: https://www.urlencoder.org/). Thus, having ID "osdu: work-product-component--WellboreMarkerSet:3D%20Kirchhoff%20DepthMigration" (with %20 combination) you should url-encode it and request "osdu%3Awork-product-component--WellboreMarkerSet%3A3D%2520Kirchhoff%2520DepthMigration" instead.
Configuring mappers Datasources
When using non-Google-Cloud-native technologies, property sets must be defined on the Partition service as part of PartitionInfo for each Tenant.
For OQM RabbitMQ
prefix: oqm.rabbitmq
It can be overridden by:
- through the Spring Boot property
oqm.rabbitmq.partition-properties-prefix - environment variable `OQM_RABBITMQ_PARTITION_PROPERTIES_PREFIX``
Propertyset (for two types of connection: messaging and admin operations):
| Property | Description |
|---|---|
| oqm.rabbitmq.amqp.host | messaging hostnameorIP |
| oqm.rabbitmq.amqp.port | - port |
| oqm.rabbitmq.amqp.path | - path |
| oqm.rabbitmq.amqp.username | - username |
| oqm.rabbitmq.amqp.password | - password |
| oqm.rabbitmq.admin.schema | admin host schema |
| oqm.rabbitmq.admin.host | - host name |
| oqm.rabbitmq.admin.port | - port |
| oqm.rabbitmq.admin.path | - path |
| oqm.rabbitmq.admin.username | - username |
| oqm.rabbitmq.admin.password | - password |
Example of a single tenant definition
curl -L -X PATCH 'https://dev.osdu.club/api/partition/v1/partitions/opendes' -H 'data-partition-id: opendes' -H 'Authorization: Bearer ...' -H 'Content-Type: application/json' --data-raw '{
"properties": {
"oqm.rabbitmq.amqp.host": {
"sensitive": false,
"value": "localhost"
},
"oqm.rabbitmq.amqp.port": {
"sensitive": false,
"value": "5672"
},
"oqm.rabbitmq.amqp.path": {
"sensitive": false,
"value": ""
},
"oqm.rabbitmq.amqp.username": {
"sensitive": false,
"value": "guest"
},
"oqm.rabbitmq.amqp.password": {
"sensitive": true,
"value": "guest"
},
"oqm.rabbitmq.admin.schema": {
"sensitive": false,
"value": "http"
},
"oqm.rabbitmq.admin.host": {
"sensitive": false,
"value": "localhost"
},
"oqm.rabbitmq.admin.port": {
"sensitive": false,
"value": "9002"
},
"oqm.rabbitmq.admin.path": {
"sensitive": false,
"value": "/api"
},
"oqm.rabbitmq.admin.username": {
"sensitive": false,
"value": "guest"
},
"oqm.rabbitmq.admin.password": {
"sensitive": true,
"value": "guest"
}
}
}'
Exchanges and queues configuration
At RabbitMq should be created exchange with name:
name: register-subscriber-control
It can be overridden by:
- through the Spring Boot property
oqm-register-subscriber-control-topic-name - environment variable
OQM_REGISTER_SUBSCRIBER_CONTROL_TOPIC_NAME
Interaction with message brokers
Specifics of work through PULL subscription
To receive messages from brokers, this solution uses the PULL-subscriber mechanism to get 'record_changed' messages. This is its cardinal difference from other implementations that use PUSH-subscribers (webhooks). This opens a wide choice when choosing brokers.
When using PULL-subscribers, there is a need to restore Storage service subscribers at the start of Storage service.
This magic happens in the OqmSubscriberManager.java class from core-lib-gcp in the @PostConstruct method.
Keycloak configuration
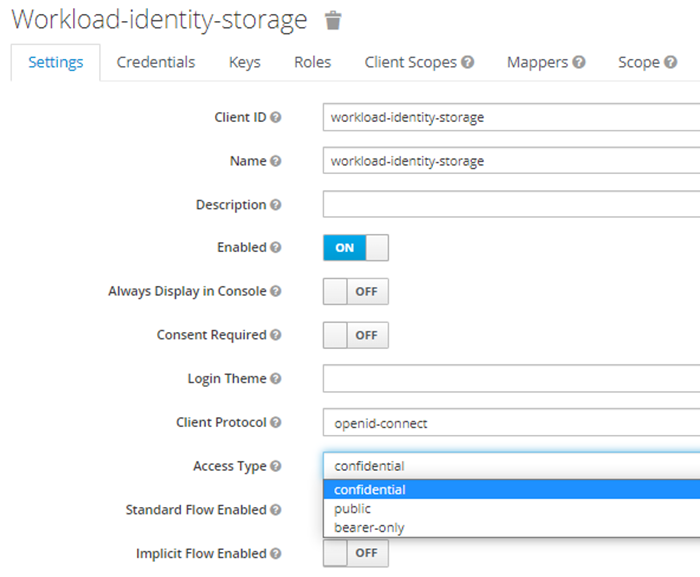
Keycloak service accounts setup
Configure Clients. One Client per OSDU service. Set them “confidential”.
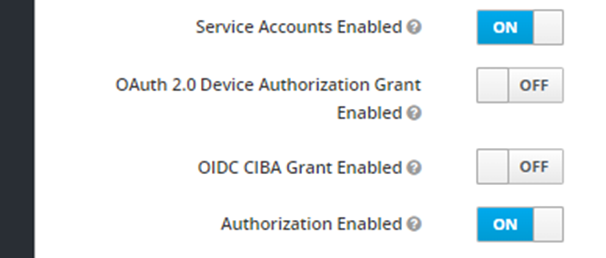
Each Client has embedded Service Account (SA) option. Enable SAs for Clients, make “Authorization enabled”:
Add partition-and-entitlements scope to Default Client Scopes and generate Keys.
Give client-id and client-secret to services, which should be authorized within the platform.